AI agent analytics is the practice of quantifying, comparing, and explaining how autonomous agents behave end to end. It turns raw events from models, tools, and orchestration into answers buyers actually need: which execution paths drive cost and latency, where reasoning drifts, whether multi-step goals succeed, and whether improvements hold at production scale. Without that layer, product and ops teams are stuck reconciling ad hoc logs with quarterly business reviews, while engineering burns cycles on issues that no aggregate metric exposes.
The business risk is not merely model inaccuracy. Agents string together retrieval, planning, and tool use; a subtle mistake early in a trajectory can look acceptable at each local step and still fail the user or the workflow. Stakeholder trust, incident time, and vendor spend all hinge on whether you can analyze behavior at the right level of resolution and tie it to remediation.
Enterprise deployment adds procurement pressure. You are buying software that will hold prompts, tool payloads, and identifiers under retention policies that differ by region, customer contract, and internal security rules. The sections below start from what breaks when teams treat agent analytics as chat logs or classic application performance monitoring (APM), then move to evaluation requirements, common buying mistakes, and security and governance constraints.
TL;DR
- Buy analytics that support span, trace, and session views of the same underlying telemetry—not a single canned dashboard—so you can diagnose failures at every level of agent complexity.
- Require open, portable instrumentation and exportable evaluation artifacts so you are not locked into a vendor’s metric definitions and can move your data if your stack changes.
- Budget for the full data path: storage, reprocessing, eval compute, and human review loops when labels matter, so costs don’t surprise you after you’ve committed to a contract.
- Separate gateway convenience from in-process visibility if your agents are safety- or contract-critical, so architecture choices don’t leave your reasoning logic invisible.
- Tie any purchase to provable closed-loop workflows—from production signal to dataset or eval change to a measured regression or improvement window—so you can demonstrate that changes are actually working.
Why you need AI agent analytics
Most teams deploying AI agents discover the same problem: by the time something is clearly broken, they can’t explain why. Traditional dashboards show latency and error rates. They don’t show whether your agent picked the right tool, took the right path, or accomplished what the user actually needed.
Agent analytics exists because agents fail in ways that don’t look like failures. An agent can complete every step without an error and still give the wrong answer, loop unnecessarily, or cost ten times what it should. The only way to catch that is to observe behavior at the right level of detail—not just individual calls, but full trajectories and sessions.
For organizations deploying agents in production, this capability unlocks three things. First, it gives engineering teams the evidence they need to make changes with confidence rather than guessing. Second, it gives product and ops teams a shared source of truth for what agents are actually doing, which reduces the time spent reconciling anecdotal reports. Third, it gives security and compliance teams the audit trail they need when agents handle sensitive data or make consequential decisions.
Teams that can’t observe agent behavior at the trajectory level tend to discover failure through customer complaints, not dashboards.
Why traditional approaches fail for AI agent analytics
A production agent is rarely one API call. It is a policy over tools and memory, often with branching and retries. Conventional APM and request logs were built for deterministic services. They can show latency and errors at service boundaries, but they do not naturally capture which tool was chosen, whether it was the right tool, or whether a sequence of spans achieved the user’s goal. Research on long-context and multi-step use shows that local correctness does not guarantee global success. For example, Liu et al. documents how information placement in long contexts affects model use, a phenomenon that is easy to miss if you only score final answers.
The failure scenario is predictable. An agent completes every span without raising an exception—meaning no error is returned and every step technically succeeds—yet the business outcome is wrong. Support tickets rise while dashboards look green, because the metric was “no 500s” or “average answer length in range,” not “goal achieved with minimum unnecessary tool calls across the full trajectory.” Teams that rely on static offline tests alone discover another gap. Agents that pass curated suites still fail in the wild as traffic shifts, tool schemas change, and prompts drift. Static test cases are rarely sufficient when paths multiply.
Here is what that looks like in practice. A customer support agent receives a billing question and selects a product documentation retrieval tool instead of the billing records tool. The retrieved context is irrelevant, so the model re-queries with a modified prompt, pulls a second unrelated document, and enters a retry loop. By the time the session times out, the agent has made eleven tool calls, spent roughly thirty times the expected token budget, and returned an answer the user rejected. Every individual span completed without an error. Nothing in a standard dashboard flagged it. The trace, reviewed afterward, shows the wrong tool selected at step one.
Legacy observability also struggles with non-determinism. Two runs with the same nominal intent can differ at the token level, so naive diffing and fixed thresholds misfire. The bottleneck is not only data volume; it is the need for analysis units that match agent semantics, including sessions for multi-turn work and path-level structure for tool-heavy flows.
Core evaluation criteria for AI agent analytics platforms
Vendors will claim end-to-end visibility. Your job is to require capabilities that make analytics actionable for generative, multi-step systems. You want passive capture plus active engineering: the same traces must feed offline testing, online monitoring, and documented iteration.
Open standards and telemetry matter because your stack will change. Models, hosts, and frameworks will churn. A platform that only accepts a proprietary log format or a single vendor’s wire protocol creates long-term cost. The ability to map spans to a shared schema and to move evaluation definitions across tools is a procurement requirement, not a future nice-to-have.
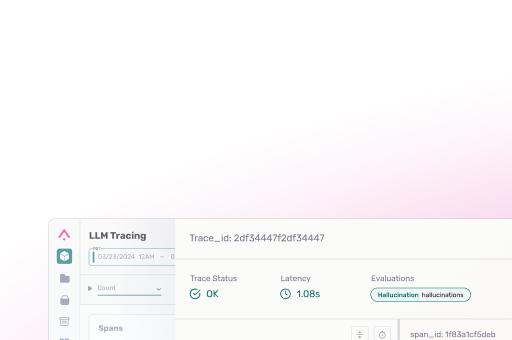
You also need evaluability that matches the shape of the work. Span-level checks catch a bad tool call. Trace-level checks ask whether the overall workflow did the right thing. Session-level checks cover coherence and goal completion for multi-turn interactions. Buyers should look for a clear object model, APIs to pull labeled or scored data for audit, and paths to run LLM-based judges and code-based checks on the same records.
Open standards and telemetry interoperability
A serious platform should expose how it ingests and represents traces and spans, including alignment with de facto standards in the LLM space and interoperability with the broader observability ecosystem. You are looking for clear documentation on how tool calls, model calls, and custom attributes are represented, and on how to export or query that data for your own analysis.
So what? If the vendor cannot answer how your data leaves their system, you are not buying analytics; you are buying a report that ends when the contract does.
Closed-loop evaluation and experimentation
The analytics product should connect what you see in production to what you can change, measure, and gate. That includes experiments and datasets tied to the same trace identifiers, so teams can compare behavior before and after a prompt, policy, or routing change, and can detect regressions on realistic workloads as well as on toy prompts.
Why this matters: when production traces never feed a structured experiment, teams optimize narratives instead of metrics. Closed-loop products reduce the time from observation to a validated change.
Agent-path and tool-use diagnostic capability
For AI agent analytics, you need to analyze trajectories—the full sequence of steps an agent takes across tools, model calls, and decisions—not just individual completions. A single model call might look fine in isolation while the overall path wastes tool calls, loops unnecessarily, or misses the user’s intent entirely. The platform should support reasoning about which paths dominate, how often tools are invoked, where loops or handoffs appear, and how that maps to cost and user outcomes. In procurement language, require demonstrations on your own or representative traces, not a canned demo with a clean graph.
So what? If the tool cannot help you see path-level failure, you will pay for aggregate charts while incidents stay unexplained on the hot path.
Ask these questions in any demo
Use the evaluation criteria above as a live checklist when you’re in front of a vendor:
- Show me how you represent a multi-step agent trace that includes both tool calls and model calls. What’s the object model?
- Can I export a scored dataset from your platform—evaluation results tied back to trace identifiers—and load it into my own tools?
- Walk me through a before-and-after experiment on a real prompt or routing change. How does your product connect production signal to a measured outcome?
- What open standards do you align to for span and trace representation? How do I get my data out if I move to a different backend?
- How does your platform handle session-level evaluation across multi-turn interactions, not just single completions?
If a vendor can’t answer these questions on real traces—or redirects to roadmap slides—that tells you what their product actually does today.
| Capability | Why it matters | What to ask | Evidence required | Deal-breaker if absent |
| Span, trace, and session views | Agents fail at different levels; you need to diagnose at each one | Show me a multi-step trace with tool calls and model calls in your UI | Live demo on representative traces, not a clean example | Yes |
| Open/exportable instrumentation | Vendor lock-in compounds when you change models or frameworks | How do I get my evaluation datasets and scored traces out of your system? | Working export or API on a real dataset | Yes |
| Closed-loop experimentation | Without it, you optimize narratives instead of metrics | Walk me through a before-and-after experiment on a real prompt change | Demonstrated regression detection on a realistic workload | Yes |
| Self-hosted / data residency options | Regulated environments may prohibit sending traces to third-party cloud | Is self-hosting available, and which subprocessors handle trace data? | Written confirmation matching your compliance requirements | Depends on environment |
Pitfalls to avoid during AI agent analytics procurement
Buyers who underestimate the difference between a gateway proxy and in-process telemetry often get fast setup and shallow reasoning visibility. A proxy can centralize model calls, but the agent’s branching logic, retries, and internal state may be invisible or coarse unless your instrumentation and backend support the same span model end to end.
Another common mistake is treating eval scores as a substitute for data governance. Scores on traces that cannot be rehydrated, exported, or audited are difficult to defend under incident review—because when something goes wrong, you need to reproduce the exact trace, not just know the average score. That distinction matters in regulated environments and is worth testing explicitly in any proof of concept.
Underestimating storage and compute is routine. Generative traffic generates nested spans; retention for compliance can multiply bytes without adding insight unless tiering, sampling policies, and aggregate rollups are agreed up front. A fourth miss is overfitting procurement to a single team. Product, security, and ML engineering rarely share one dashboard, yet one analytics contract must answer questions for all three without copy-paste silos. Finally, buying on roadmap slides instead of on shipped APIs for query and export is how teams end up with marketing analytics instead of engineering analytics.
- Proxy-only stacks can miss deep reasoning structure when your failure modes live inside the agent’s control flow.
- Pretty dashboards without queryable exports and stable identifiers block audits and post-incident forensics.
- Storing every raw prompt at full fidelity without retention and access policy alignment creates legal and cost exposure.
- Evals that are not versioned and replayable turn into unrepeatable story points under scrutiny.
- Bundling “AI analytics” with generic real user monitoring (RUM) or web analytics—tools designed to track page views and clickstreams, not multi-step agent trajectories—can dilute the schema you need for tools and trajectories.
Security, scale, and governance for AI agent analytics
Telemetry from agents often includes user text, retrieval-augmented generation (RAG) context, and tool results. The security surface is larger than a typical microservice log stream because the data is more sensitive and the blast radius of leakage includes third-party model providers, vector stores, and line-of-business systems connected via tools. OWASP’s guidance for large language model applications is a useful checklist for what can go wrong, including prompt injection, excessive agency, and unsafe outputs; your analytics and monitoring story should map to those classes with concrete controls.
Scaling the data foundation
High-cardinality, deeply nested trace data can stress ingestion, indexing, and cost controls. You need a shared understanding of what raw detail analysts need versus what aggregate metrics satisfy compliance and SRE dashboards, and for how long each tier lives in hot storage.
Continuous security testing
For agent paths that call external tools and retrieve untrusted text, you should plan adversarial and regression testing that mirrors the ways prompts and context can be abused. That includes evaluation templates that can flag policy-breaking outputs and unsafe tool arguments when those risks exist in your domain.
Compliance and trust mapping
When prompts or outputs fall under health or other regulated handling, the analytics platform must support role-based access, data residency choices where offered, and retention that matches your record-keeping obligations. If you face HIPAA-style handling, the contract and architecture should match that reality, not a generic cloud checklist. If your vendor’s SOC 2 or comparable assurance covers the subprocessors and flows you actually use, obtain that mapping in writing for security review, not as a footnote in a slide deck.
From aggregate charts to verified engineering
AI agent analytics is how teams stop arguing about individual examples and start improving systems with evidence. The shift is from passively watching outputs to running a verifiable loop across production data, evaluation logic, and change control. Arize AX and the OpenInference ecosystem are built around that idea: open-standards-friendly telemetry, evaluation, and product workflows that let you connect what you see to what you ship, without trading away portability for a short-term integration shortcut.
FAQs about AI agent analytics
How is AI agent analytics different from LLM monitoring of token latency and error rates?
LLM monitoring that stops at per-call latency and HTTP status can miss multi-step failure. Agent analytics is concerned with path structure, tool usage, session-level outcomes, and whether changes improve the behaviors you can measure at each layer.
What should a proof-of-concept demonstrate before we sign?
Require ingestion on a representative trace mix, a trace- or session-level evaluation you can re-run, export or API access to scored records, and a before-and-after experiment on a real change, not a hand-picked set of happy paths.
Which open standards or conventions should RFPs mention?
Ask how spans represent model and tool events, how context propagation works in your stack, and what export or query paths exist. Even when final choices vary, the answers separate portable designs from one-off agents.
How should we think about cost of ownership for agent analytics?
Model costs and vendor seat fees are only part of the picture. Data retention, eval compute, and human labeling for high-stakes decisions belong in the same TCO model as raw trace volume.