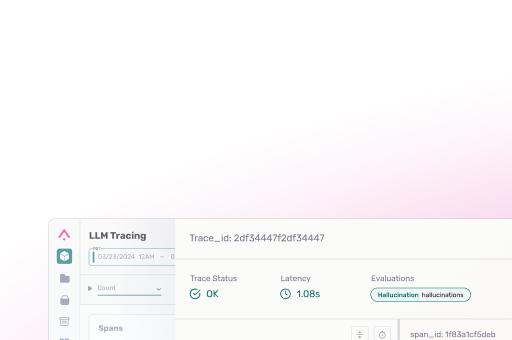
Security features at Arize start at a structural level and are deeply embedded throughout the platform. The Arize Security Periodic Table showcases the company’s rigorous operational approach to achieving audibility, prevention, and preparedness.
See how we use industry-leading practices to implement comprehensive security to protect your company and customer data, and remain confident in our ability to protect your information.