Agent observability is the discipline of making autonomous generative AI- and LLM-based systems visible: you see the chain from intent through tools, memory, and model calls to outcomes, in enough detail to debug, measure, and improve. It’s not the same as logging the last model response or charting request latency. It’s a structured view of how an agent plans, recovers, and hands work off, so teams can answer why a path was taken, not only that a path finished.
The business case is risk and velocity. When product and governance, risk, and compliance (GRC) teams cannot reconstruct what an agent did during a specific incident or under production load, every incident becomes a war room and every model or policy change becomes a guess. Stakeholders lose trust when “healthy” systems produce wrong or unsafe actions. Procurement for agent observability is therefore a bet on visibility plus evaluation: you are buying the stack that turns raw runs into reviewable evidence and into tests that stay current as your agents evolve after launch.
The sections that follow start from what fails when people map agents onto APM (application performance monitoring) and single-turn LLM monitoring, then lay out what to require in a platform, common buying mistakes, and what security and scale look like when prompts and tool payloads live in the same system of record as traces.
Why you need agent observability
Agents are making consequential decisions on behalf of your users and your business. Without structured visibility into those decisions, you are operating blind. Here is what agent observability unlocks:
- Faster debugging. When something goes wrong, you can trace exactly which tool, model call, or branch caused the failure—rather than spending hours in log files.
- Safer deployment. You can catch unsafe or unexpected actions in test environments before they reach production, reducing the risk of an incident becoming a headline.
- Credible audit trails. Compliance and legal teams can review what an agent did, why, and when—necessary for regulated industries and increasingly expected everywhere else.
- Continuous improvement. Structured traces feed evaluation pipelines that measure whether changes actually improved outcomes, so you ship with confidence rather than hope.
- Stakeholder trust. When leadership, customers, or auditors ask “what did the agent do here?”—you have an answer.
TL;DR
- Require full execution graphs, not just token or endpoint metrics: tools, branches, and handoffs must be first-class in the trace model, so you can reconstruct any failure end to end.
- Anchor procurement on open wire formats and span semantics you can export; framework-native consoles alone are a long-term data silo that will cost you when you want to switch vendors or run your own analysis.
- Buy for span, trace, and session views of the same telemetry, with evals that can run at each layer, so you can find failures that only appear across multiple turns.
- Treat proxy-only capture as a conscious trade: it may be fast to adopt but shallow on reasoning structure, leaving you blind to in-process branching and retry logic.
- Tie any purchase to provable closed-loop workflows: from production signal to dataset or eval change to a measured before-and-after, so you can show that the tool actually improves outcomes—not just dashboards.
Why traditional approaches fail for agent observability
An AI agent is software that can take sequences of actions autonomously—calling external tools, querying databases, invoking other models, and making decisions based on those results—rather than returning a single answer to a single question. That autonomous, multi-step structure is what makes agents powerful, and it is exactly what makes them hard to observe with standard approaches.
Classic application performance monitoring (APM) assumes stable service boundaries and meaningful HTTP status codes. An agent can return 200s while following a plan that produces harmful or wrong outputs. APM tells you the service is alive; it tells you nothing about whether the agent is working.
Why this matters for procurement:
- Dashboards can show low error rates while support and RevOps teams file tickets about bad outcomes.
- Teams end up with logs of API calls, not a replayable graph of which tool ran, in what order, and why a branch was taken.
- “Legacy LLM monitoring” that centers on input-output pairs also breaks down. Agents are not a single completion: they are sequences of decisions. Observability for agents has to follow that sequence, not treat each call as independent.
Examples of failures observability should catch
- Bad branch: The trace shows the agent chose plan B after a tool error, but dashboards only show “200 OK” on the API—so you can’t explain why a customer saw the wrong outcome.
- Hidden retry loop: The agent retries the same tool call with escalating prompts; latency and cost spike while “success rate” looks fine—so you can stop runaway spend before it hits production budgets.
- Unsafe tool call: A prompt-injection path triggers a tool with arguments you wouldn’t approve—so you can block or redact before data leaves the trust boundary.
- Sub-agent handoff failure: Work passes to a sub-agent that drops context or duplicates steps—so you can see which handoff broke and replay from the last good span.
Core evaluation criteria for agent observability platforms
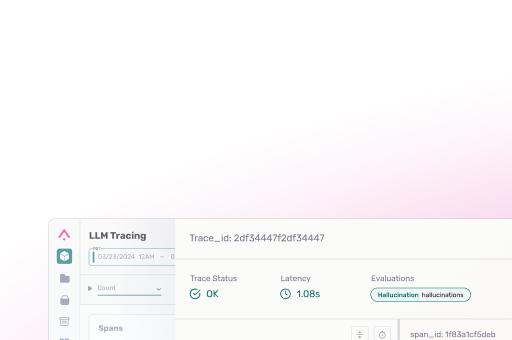
Procurement should filter on whether a product was built to trace reasoning structure, not only to store prompts. You want a clear position on how spans represent tool calls, model calls, and custom steps, regardless of which orchestration framework generated them.
You also need evaluation that lines up with how agents fail: at the span, across a trace, and across a user session. A platform that only visualizes but never scores, or that scores only offline rows without a path back to production, will require a second product to close the loop.
Open standards and telemetry interoperability
Why this matters for buyers: agent workloads churn faster than typical SaaS apps—frameworks, model APIs, and evaluators change quarterly. If your traces are locked in a proprietary shape, every roadmap bump becomes a migration project; open semantics and export let security, data, and platform teams agree on what “one run” means and keep evidence portable if you change vendors.
Ask how traces are produced and how they leave the vendor’s solution. De facto standards in the LLM space and alignment with the broader OpenTelemetry ecosystem reduce the odds that you are buying a pretty UI on top of a proprietary format that locks your data in.
If the answer to “how do I export this to our warehouse or replay it in another tool?” is a PDF and a professional services line item, you do not have observability; you have a report.
Closed-loop evaluation and experimentation
Observability that stops at a trace viewer still leaves change management as guesswork. The product should connect traces to experiments, datasets, and deployment gates: same IDs, same schema, so a regression in production becomes a reproducible test case, not a ticket. Offline suites help, but only if the data they run on comes from live traffic and feeds back into live decisions.
If production never feeds structured experiments, the vendor relationship devolves into dashboard theater while incidents repeat.
Multi-agent, runtime, and tool-path visibility
Agent observability has to cover path-level structure: which node or role fired, when handoffs happen, and how tool traffic concentrates. In procurement, ask for live demonstrations on your own traces (or representative ones), not pre-recorded walkthroughs.
If the tool cannot show path and handoff structure on representative traffic, you will be blind exactly where production agents are most likely to fail.
What a good agent trace should show
Use this as a checklist—each item should be visible, searchable, and exportable in the vendor’s trace model:
- User intent (request / goal as the agent understood it)
- Model calls (which model, versions, key parameters)
- Tool calls (name, arguments, results, errors)
- Inputs and outputs for each step (with redaction rules documented)
- Retries (count, backoff, what changed between attempts)
- Branches (which decision sent execution down which path)
- Handoffs (parent ↔ sub-agent, including session/thread IDs)
- Latency per span and end-to-end
- Token and cost attribution per step where available
- Eval scores attached to traces or spans you care about
- Session ID (stable grouping across turns)
- Exportable identifiers (trace ID, span IDs, correlation IDs) that match your warehouse and incident tooling
Questions to ask vendors
- Can you show me a trace from my own agents—not a canned demo—during the proof of concept?
- How are spans structured for tool calls, sub-agent handoffs, and retries? Show me the schema.
- What does export look like? Can I replay a session in another tool or push scored records to our warehouse?
- How does a production failure become a reproducible test case in your platform?
- What open standards do you support, and what happens to my data if I stop using you?
Pitfalls to avoid during agent observability procurement
The most expensive mistake is confusing gateway convenience for full-process visibility. A proxy in front of model calls can be quick to wire, but the branching logic, retries, and in-process state that define agent behavior happen inside the runtime—not at the gateway.
A second mistake is underestimating data volume: nested spans from tools and sub-agents multiply cost and retention work.
A third is signing for “AI observability” that is really web or infrastructure metrics with an LLM label attached, for example:
- Proxy-based capture without a plan for in-depth spans can hide control-flow failures.
- Storing irreplaceable raw prompts without a tiering and access model aligned to legal and infosec review.
- Relying on a vendor metric catalog you cannot recompute elsewhere when models or evaluators change.
- Skipping session-level view when the product is conversational or multi-turn by design.
- Running a bake-off only on simple development traffic that avoids the long tool chains or multi-agent handoffs your production agents will actually use—which means you will not see failures until after you have signed.
Security, scale, and governance for agent observability
Traces that capture prompts, tool I/O, and user identifiers are sensitive by construction. The blast radius includes model vendors, retrievers, and line-of-business systems reached through tools. OWASP’s Top 10 for large language model applications names prompt injection, insecure tool execution, and data leakage as live risks—all of which surface in traces before they surface in incidents.
Scaling the data foundation
Long-running, multi-tool agents can emit high-cardinality, deeply nested data. You need a shared model of who needs raw traces versus aggregates, how long each tier is retained, and what incident response actually queries when something goes wrong at 2 a.m. Cost and compliance both push toward clarity here, not “store everything forever because disk is cheap.”
Continuous security testing
For agents that use tools against untrusted text or the open web, observability should pair with test and red-team patterns that exercise abuse paths, not only happy calls. That includes evaluation or policy hooks that can flag disallowed content or tool arguments in environments where a mistake is a headline.
Compliance and trust mapping
If your system handles health or other regulated data in prompts or outputs, role-based access, region choices, and documented subprocessors are not “nice to have” sections. When HIPAA-style handling is in play, architecture and contract need to line up, not a generic “we are serious about security” paragraph. Ask how SOC 2 (or equivalent) coverage applies to the components you actually use, in writing, before you standardize a pipeline on a vendor’s collectors.
Closing the loop on production agents
The shift you want is from opaque heroics to repeatable engineering. Agent observability is the substrate: structured traces, portable semantics, and evaluation that can ride the same data your teams already use to debug. Arize AX and the OpenInference ecosystem are aimed at that stack: connect what you see in live traffic to what you can test and ship, with room to move as frameworks and runtimes change underneath you.
FAQs about agent observability
How is agent observability different from APM and from basic LLM monitoring?
APM optimizes service health; basic LLM monitoring often stops at per-call input/output. Agent observability is about the reasoning and tool path between them: which steps ran, in what order, and whether the chain satisfied the user’s goal.
What should a proof of concept require before we sign?
Require ingestion and visualization on your own or representative traffic, a trace- or session-level eval you can re-run, export of scored records, and a before-and-after on a real change, not a curated happy path.
How do open standards like OpenTelemetry and OpenInference fit a buyer stack?
You want documented span shapes and export paths. Standards reduce lock-in to any one host framework and make it easier to align security operations and data teams on what “a trace” means in audits.
Why are session-level views part of agent observability?
Many failures only show up across turns. Session-level groupings and evaluations ask whether a conversation achieved its goal, not whether each model call looked acceptable in isolation.